Database passthrough authentication for Databricks
This feature is currently in open beta for Databricks with support for additional databases to be implemented. Please contact us to get access to the beta program.
Introduction
Database passthrough authentication enables organizations to enforce data security policies directly at the data warehouse level, rather than managing them within individual applications.
- Centralized Security Management: Apply consistent data security policies across all your applications and tools
- Granular Access Control: Leverage your existing role-based access controls (RBAC) directly from your data warehouse
- Reduced Maintenance: Eliminate duplicate security configurations across multiple data tools
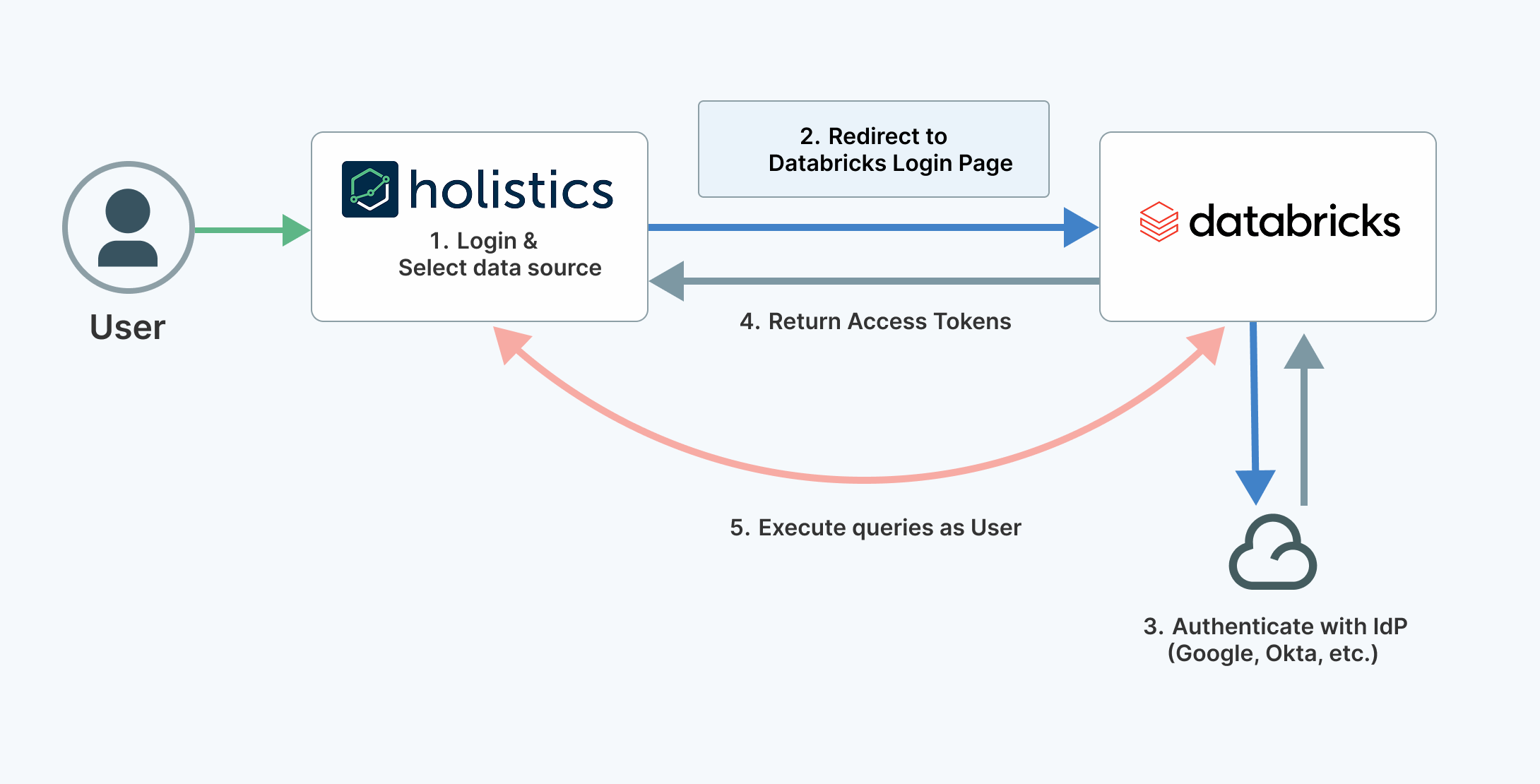
How it works
When users access data through Holistics, they authenticate using their individual Databricks credentials. This ensures that data access permissions are enforced at the source, maintaining your organization's security policies.
Step-by-step setup
Step 1: register Holistics as a custom OAuth application in Databricks
-
Follow the Databricks documentation to enable custom OAuth applications
-
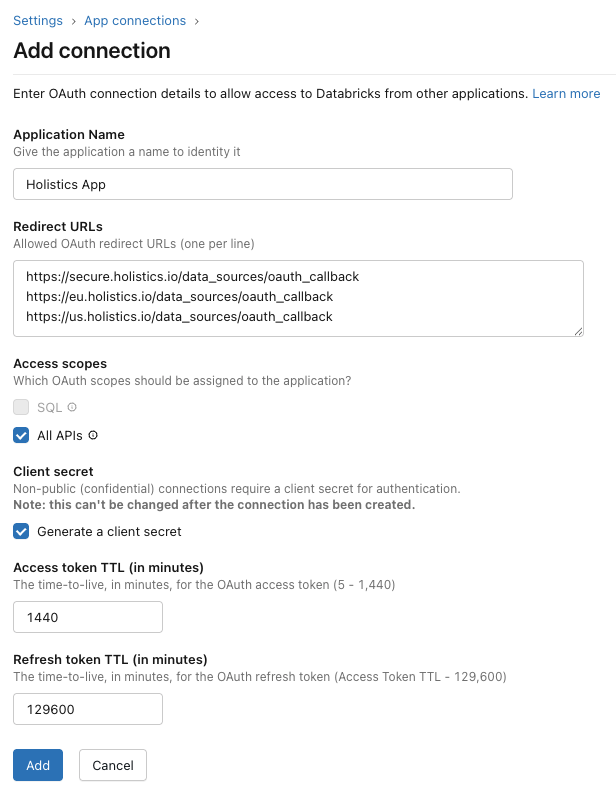
Configure the following settings on the "Add Connection" page:
Redirect URLs:
https://secure.holistics.io/data_sources/oauth_callback
https://eu.holistics.io/data_sources/oauth_callback
https://us.holistics.io/data_sources/oauth_callback
Note: If you're using a custom domain e.g. company.holistics.io, please add the custom domain to the redirect URLs following the pattern above.
e.g. https://company.holistics.io/data_sources/oauth_callback
Additional Settings:
- Access Scopes: All APIs
- Client Secret: Enable "Generate a client secret"
- Access Token TTL: 1440 minutes (24 hours)
- Refresh Token TTL: 129600 minutes (90 days)
- After creating the application, copy and save both the Client ID and Client Secret - you'll need these in the next step.
Step 2: configure passthrough authentication in Holistics
-
Navigate to the Data Sources page in Holistics (
/manage/data_sources) -
If you don't already have a Databricks data source, add a new data source using your Personal Access Token
-
Enable passthrough authentication by clicking the "Passthrough" button on your data source in the listing page

- Enter the Client ID and Client Secret from Step 1, then save
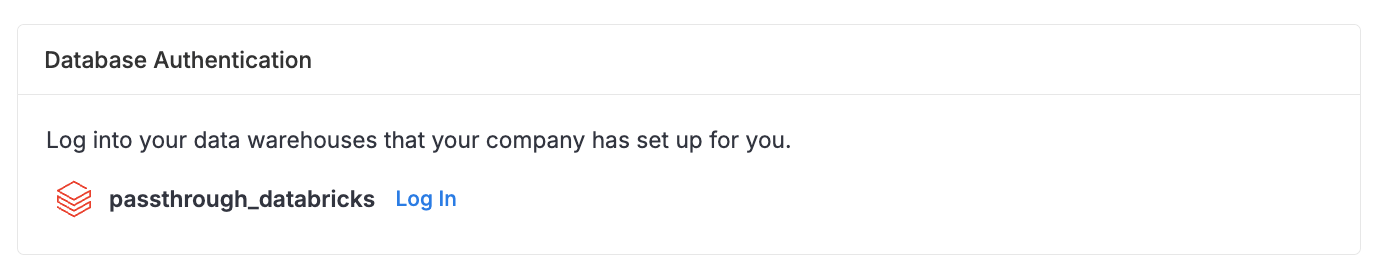
Step 3: connect your database credentials
Each user must authenticate with their individual Databricks account:
- Go to My Account settings (
/users/settings) - Locate the Database Authentication section
- Click to login with your Databricks credentials
Impacted features
Once configured, passthrough authentication will be used for:
- Viewing dashboards
- Exploring dashboard data
- Exploring datasets and data models
- Running SQL queries in the query editor
- Viewing filter suggestion values
- Scheduled deliveries (Email, Slack, Google Sheets)
- Data alerts and webhooks
- Direct data exports (Excel, CSV)
The following features are not compatible with passthrough authentication:
Frequently asked questions
How does passthrough authentication affect data caching?
Each user maintains their own private cache, ensuring data security and isolation.
Can I use both shared credentials and personal authentication simultaneously?
No. When passthrough authentication is enabled, Holistics exclusively uses personal credentials to ensure consistent and secure data access.
How are user credentials secured within Holistics?
All credentials are encrypted using AES-256 encryption and stored securely in the Holistics database.
What happens if a user's database access is revoked?
The user will immediately lose the ability to execute new queries. However, they may still view previously cached data until the cache expires.
What is the token expiration behavior?
Access tokens expire after 24 hours, and refresh tokens expire after 90 days. Users will be prompted to re-authenticate when their refresh tokens expire.